Injecting an AWS Role
AWS roles can be used to assign permissions to various AWS services. Injecting an AWS role can help understand the impact of one of these roles being compromised.
Example
What would happen if someone hacked into our web application running on that EC2 instance?
Users can inject an AWS role into a pentest by running NodeZero on an EC2 instance and assigning that EC2 instance an IAM instance profile.
When the pentest starts, NodeZero will query the IMDS and treat the EC2 instance role as an injected credential. By injecting an AWS credential, all cloud resources belonging to the associated AWS ID will be considered in scope.
Since an EC2 instance can only have one IAM instance profile assigned, and because an IAM instance profile can only contain one role, it is only possible to inject one AWS role per pentest.
Creating an IAM Instance Profile
An instance profile is what attaches an AWS role to an EC2 instance.
If you create an AWS Role in the AWS Management Console for an EC2 instance (assign the EC2 service as the trusted entity) an IAM instance profile with the same name will also be created. This means that often you do not need to manually create an IAM instance profile.
If you created the AWS Role with the AWS CLI or if the role was not created for an EC2 instance you will need to manually create an IAM instance profile.
To manually create an IAM instance profile you will need to use the AWS CLI.
The commands below show how you would create an IAM instance for a role named ExampleRole.
aws iam create-instance-profile --instance-profile-name ExampleRole
aws iam add-role-to-instance-profile --instance-profile-name ExampleRole --role-name ExampleRole
Tip
The role assigned to the instance profile must have the EC2 service specified in the trust relationship policy.
Assigning an IAM Instance Profile to an EC2 Instance
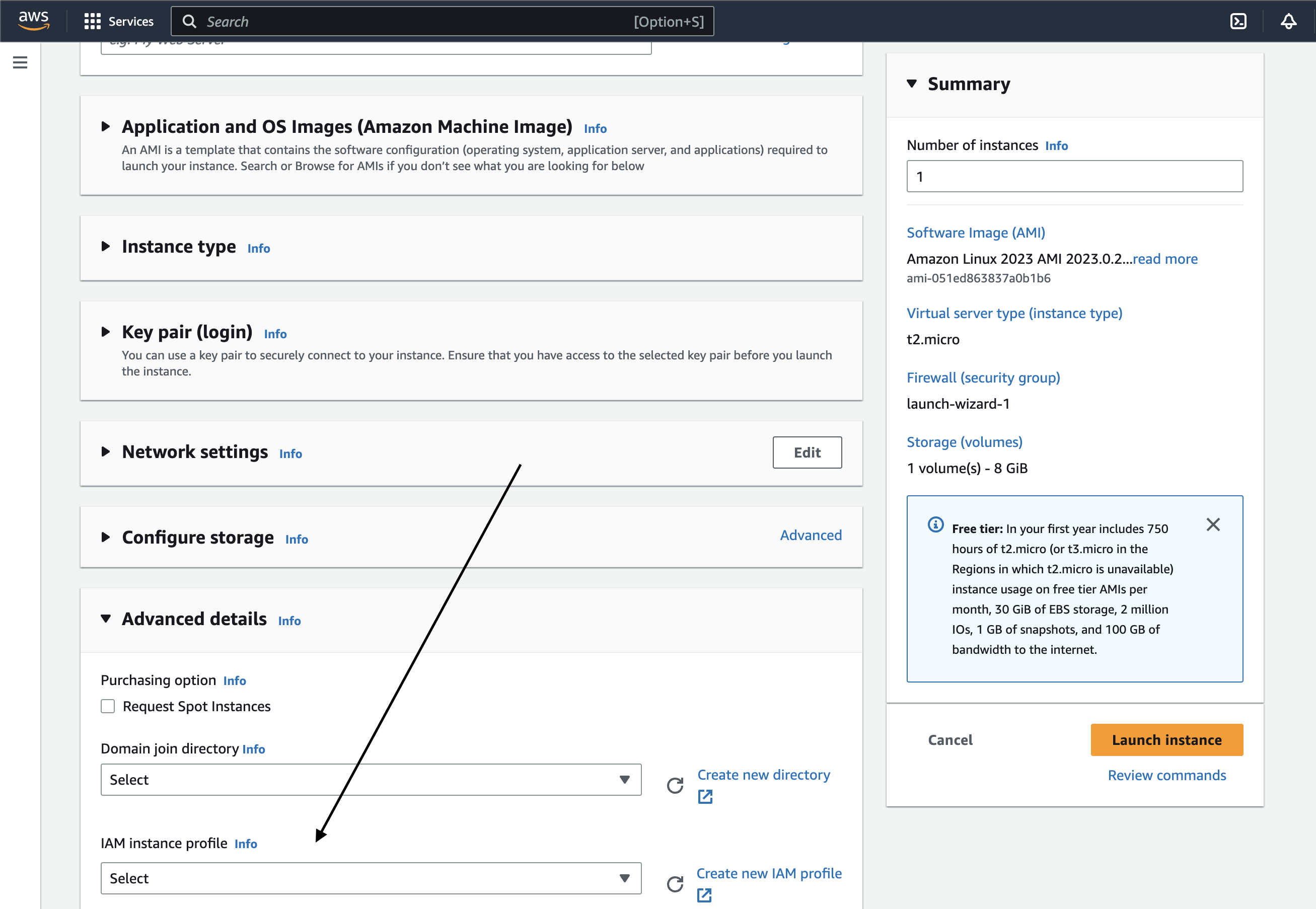
Method 1 - AWS Management Console - Assign Instance Profile when Launching a New Instance
Launch a new EC2 instance using the Launch an instance flow, find the Advanced details section and select an IAM instance profile from the drop-down.
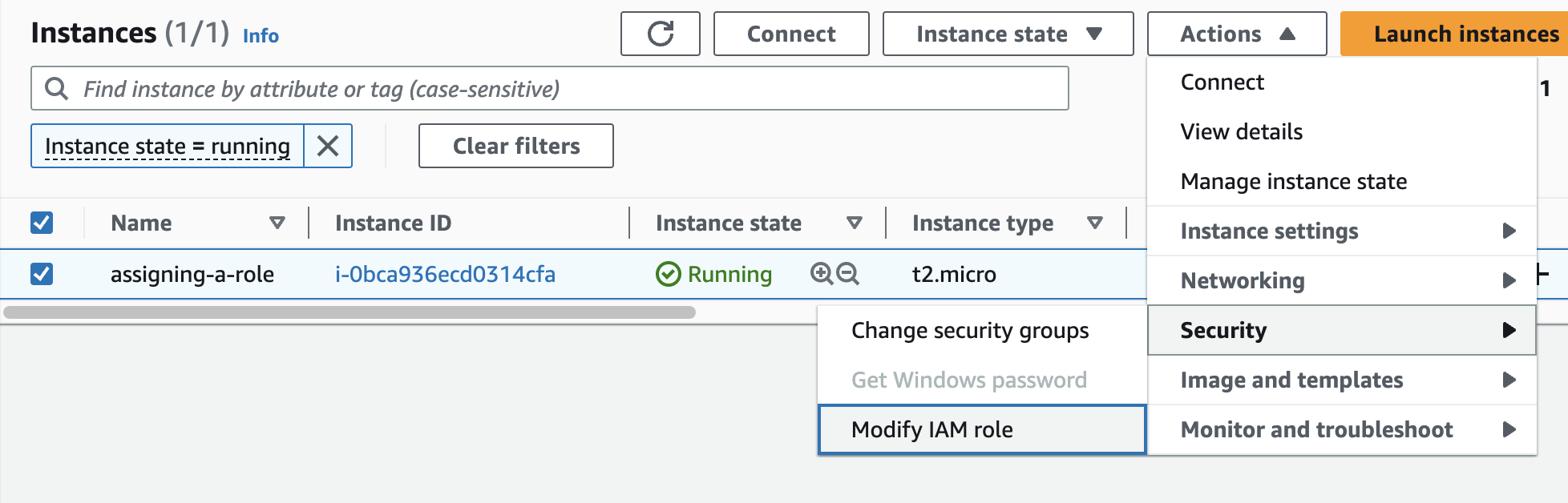
Method 2a - Assign Instance Profile to an Existing EC2 Instance - AWS Management Console
From the EC2 Dashboard or from the Instance Details page select an EC2 instance, click the Actions drop-down menu, click the Security sub-menu, and finally select Modify IAM Role.
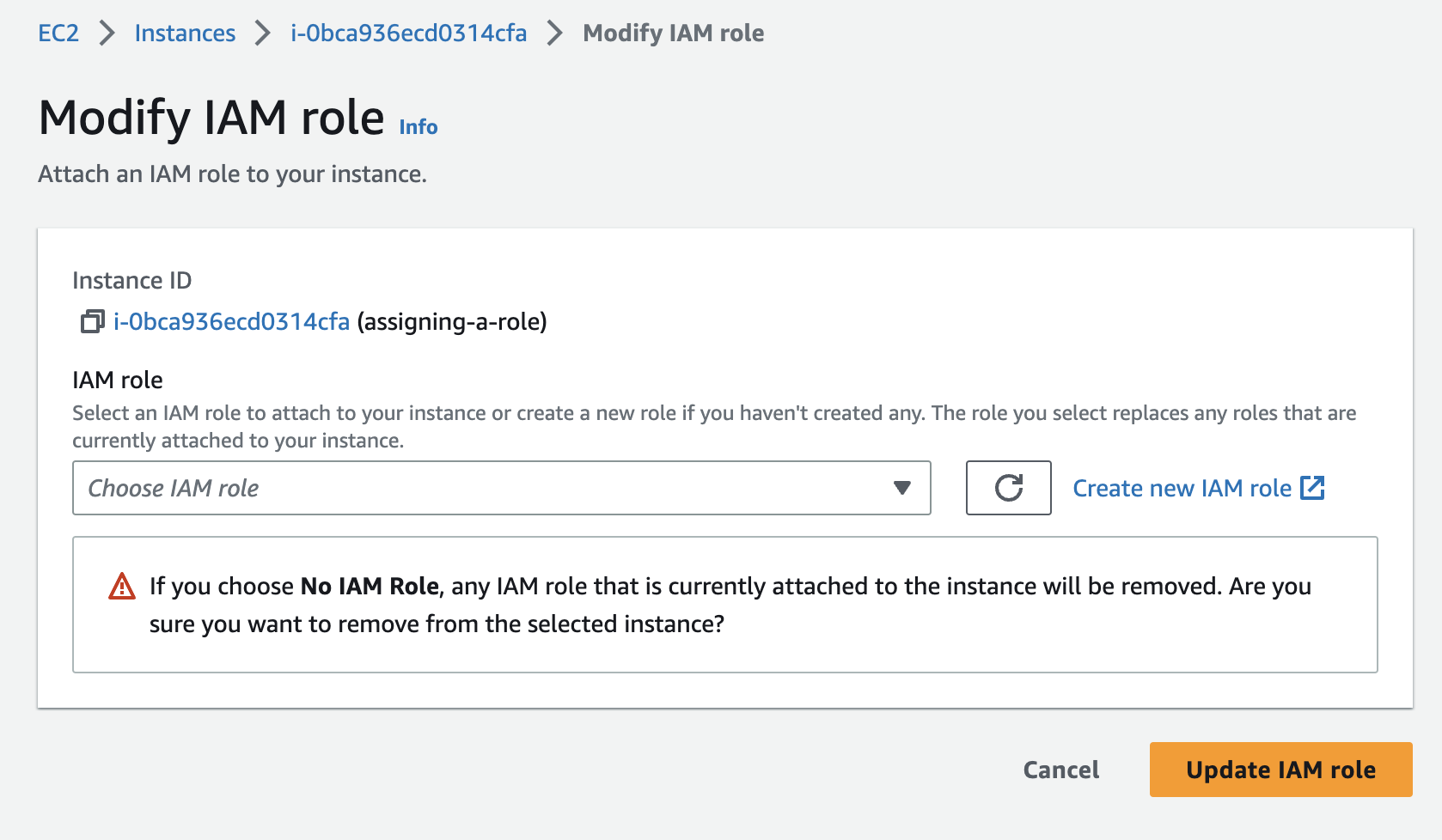
From the Modify IAM role page, select the IAM role you want to inject from the drop-down and click Update IAM role.
Method 2b - Assign Instance Profile to an Existing EC2 Instance - AWS CLI
AWS CLI Command:
aws ec2 associate-iam-instance-profile --instance-id i-123456789abcde123 --iam-instance-profile Name=admin-role